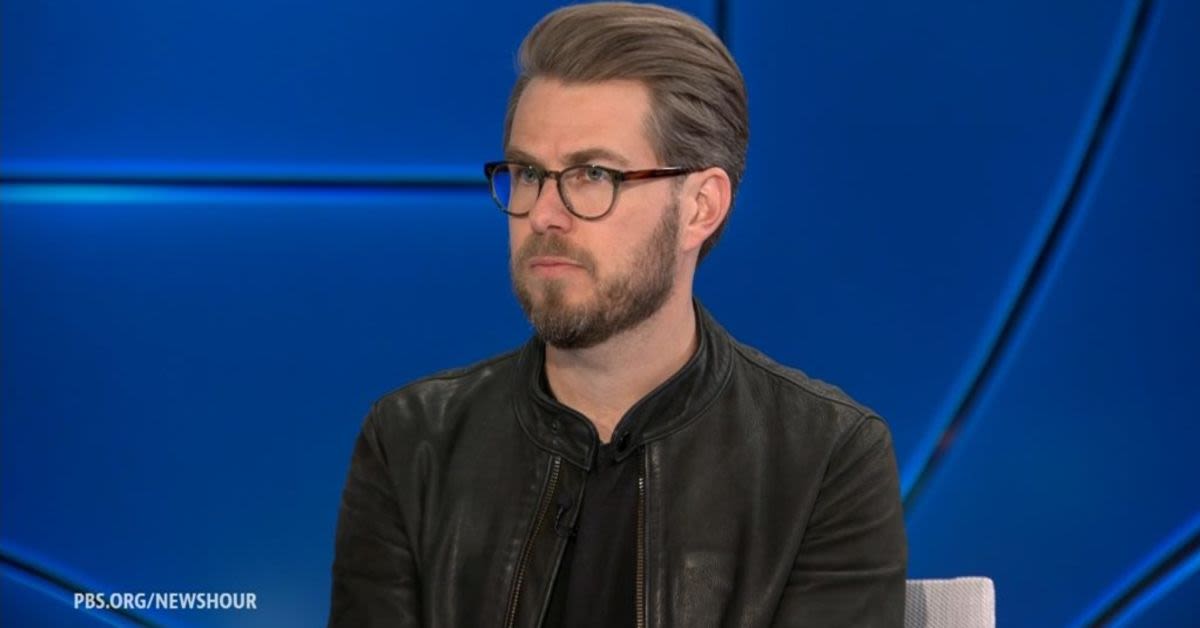
Miles Taylor, the former Trump administration official who dramatically revealed himself as the anonymous author of a 2018 anti-Trump op-ed, has now managed to expose thousands of his own supporters in a spectacular failure of basic digital security.
The onetime Department of Homeland Security chief of staff, long celebrated in establishment media circles for declaring I Am Part of the Resistance Inside the Trump Administration, has resurfaced with a new project aimed squarely at undermining Immigration and Customs Enforcement. According to Western Journal, Taylor launched a website called GTFOICE.org short for Get the Facilities Out, ICE with the stated goal of mobilizing activists to block new ICE detention centers before they open, only to end up doxing more than 17,000 of the very people who signed up to help him.
Taylor first rose to prominence in September 2018, when The New York Times published his anonymous op-ed, which it touted as the work of a senior official inside the Trump administration. In that piece, the author boasted, The dilemma which he does not fully grasp is that many of the senior officials in his own administration are working diligently from within to frustrate parts of his agenda and his worst inclinations. I would know. I am one of them.
The op-ed went on to insist that this internal sabotage was somehow noble and patriotic, even as it openly described unelected bureaucrats thwarting the agenda of a duly elected president. To be clear, ours is not the popular resistance of the left, the anonymous writer claimed. We want the administration to succeed and think that many of its policies have already made America safer and more prosperous.
Yet the author then pivoted to a familiar Beltway rationalization for defying the voters will, casting himself and his allies as guardians of the republic against the very president they served. But we believe our first duty is to this country, and the president continues to act in a manner that is detrimental to the health of our republic, the piece declared, in language that fueled fevered speculation about which high-ranking official had penned it.
For months, pundits and political junkies obsessed over the mystery, with some even suggesting thenVice President Mike Pence because of the op-eds use of the word lodestar, a term Pence had employed in speeches. When Taylor finally stepped forward in 2020 and admitted he was the author, the national reaction was less shock than confusion, as many Americans responded with a collective Wait, who? upon learning that the supposed senior insider was the chief of staff to DHS Secretary Kirstjen Nielsen.
Despite the underwhelming reveal, Taylor parlayed his moment of notoriety into a new public persona as a security expert, a label that now appears prominently in his online biographies. His Wikipedia entry distinguishes him from others with the same name by identifying him as Miles Taylor (security expert), not Miles Taylor (anonymous op-ed writer), underscoring how he has tried to recast himself as a serious authority on national and cyber security.
That makes his latest venture all the more embarrassing. Taylors GTFOICE.org project, as described by Newsweek and other outlets, was designed as a digital tool to crowd cancel ICE detention facilities by alerting local communities to proposed centers and organizing protests before they could open. We want to make sure that the moment that ICE decides to open up a new prison camp, that local communities immediately have the chance to weigh in and to stop it, Taylor told Newsweek, using the loaded phrase prison camp to describe lawful detention facilities for illegal immigrants.
Taylor insisted that GTFOICE.org stood for Get the Facilities Out, ICE, a sanitized backronym that conveniently avoids the vulgar phrase most Americans associate with those four letters. The site invited activists to sign up with their personal information so they could be notified about new ICE projects in their area and mobilized to oppose them, a mission squarely aligned with the broader left-wing campaign to hamstring immigration enforcement.
But as of this weekend, GTFOICE.org is offline, and not because Taylors campaign succeeded in shutting down any ICE facilities. Instead, the site had to be pulled after it was revealed that the personal data of everyone who signed up more than 17,000 people had been left exposed on a public interface, easily accessible to anyone who knew where to look.
Conservative commentator Jennica DataRepublican Pounds was among the first to highlight the debacle, posting a detailed breakdown on X, formerly Twitter. The sign-up data is exposed on a public REST API. No true authentication. No rate limiting. Full records: names, emails, phone numbers, zip codes, timestamps, she wrote, describing a level of negligence that would embarrass a novice web developer, let alone a self-styled security professional.
Pounds underscored the irony by contrasting Taylors rsum with his amateurish handling of sensitive data. The man who ran the third-largest federal department (250,000 employees, $60 billion budget) who oversaw election security architecture and led counterterrorism operations, then served as Googles Head of National Security Policycant secure a sign-up form, she noted, adding that he does milk hundreds of thousands of NGO dollars on these credentials. While freeloading off his fame as the person who wrote the infamous NYT article I Am Part of the Resistance Inside the Trump Administration.
For readers less familiar with technical jargon, the problem is straightforward and damning. When users submit personal information to a website, that data is supposed to be stored securely on the backend, shielded from public view and protected by authentication and other safeguards, with breaches typically occurring only when hackers manage to penetrate those defenses.
In this case, however, the data were not stolen through some sophisticated cyberattack but left sitting in plain sight on a public REST API, meaning the information was effectively published for anyone with minimal technical knowledge to retrieve. The exposure was not the result of a determined adversary but of basic incompetence in the sites design, a failure that undermines Taylors carefully cultivated image as a seasoned security hand.
The episode raises an obvious question about whether Taylors security expert label is anything more than a marketing device attached to his anti-Trump celebrity. Either his online biography should be amended to Miles Taylor (really terrible security expert), or he deliberately intended for this data to be easily discoverable, a possibility that seems unlikely given the swift decision to take the site offline once the problem was publicized.
For the thousands of activists who trusted Taylor with their personal information in the hope of helping him target ICE facilities, the fallout is a bitter lesson in the risks of signing up for ideologically driven tech projects run by political operatives rather than professionals. Many of these same activists have cheered efforts to expose and harass law enforcement officers, including ICE agents, whose identities are often concealed precisely because of threats from radical opponents of immigration enforcement.
In that context, there is a certain rough symmetry to the fact that a campaign aimed at crowd canceling ICE has instead resulted in the mass exposure of its own supporters data. At a time when officers on the front lines of border security often have to hide their faces to protect their families from retaliation, the spectacle of anti-ICE activists being inadvertently doxed by their own leader underscores the hazards of politicizing security while ignoring its fundamentals.
Login